Stanford is in the process of notifying some 200 people — a mix of employees and former students — that their privacy may have been breached due to incorrect settings in one of the University’s file-sharing systems.
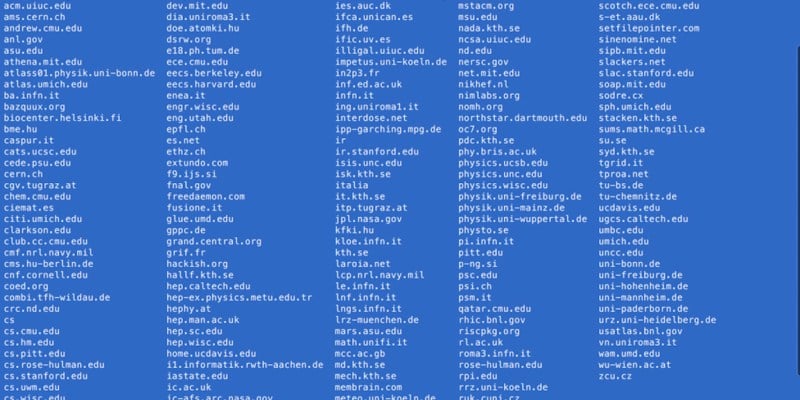
Until this week, files including sexual violence records based on counseling sessions, confidential University statistics and emails to the Office of Judicial Affairs — some with names and email addresses attached — were left broadly available on an internet server that students, faculty and staff from over 50 institutions regularly use. Any Stanford faculty, student or staff member with a SUNet ID was able to access the sensitive files; The Daily also found that an MIT student username and password were able to grant access.
The University was unaware of the data breach until it was notified by The Daily last Thursday. The Daily withheld reporting on the leak until the University secured all confidential information and notified affected parties.
“This is absolutely unacceptable and the campus is working diligently and urgently to assure that shared files are secure throughout the university,” wrote Stanford spokesperson Lisa Lapin in an official statement Thursday. “A thorough university investigation is under way as to the extent and duration of the file exposure.”
“We extend the deepest apology to the employees and former Stanford students who expected that their personal information would be treated with the greatest care by campus offices,” she added.
Stanford has used the Andrew File System (AFS) directory, where the sensitive information was until recently kept unlocked, since the 1990s. Every user with a SUNet ID is allotted 5 GB of data for personal storage and may also use the file system to access course materials and other resources.
But the sprawling server — home to over two decades of information from a range of departments in the University — compromised, among other data, 247 emails addressed to the Office of Judicial Affairs and at least 38 files recording confidential information on crimes, mostly sexual assaults, described to campus mental health counselors, the Office of Community Standards and other groups. The latter information on sexual violence was intended for tracking and reporting under the 1990 Clery Act, which mandates disclosure of campus crime.
Michael Duff, assistant vice president and chief information security officer, said that while the University can track overall AFS activity, it cannot track who has accessed specific files and folders. He said University IT also can not yet determine exactly how long many files intended for privacy were accessible for.
Compromised personal data
Within each directory, some folders and files were secured against general user access, even as the Clery files and confidential emails were left open to Stanford community members as well as people from the many other organizations that use AFS.
In the Vice Provost of Student Affairs (VPSA) directory, a file containing emails addressed to the Office of Judicial Affairs detailed concerns ranging from spousal assault to Honor Code violations to a discrimination complaint against a current faculty member. All correspondence included contact information for the sender, revealing names, email addresses and often phone numbers.
One of the Clery files also included the name and email address of the reporting party.
Most of the other Clery documents omitted names, noting instead basic demographic information such as gender, age, class year and ethnicity, as well as the accused student’s group affiliation at Stanford, in addition to a summary of what they reported.
But in a community the size of Stanford, data can be identifying even without names. Some of the documents described victim and assailant as narrowly defined as a pair of roommates of a certain class year living in a specific dormitory, or a student of a specific age and ethnicity assaulted by an upperclassman in a particular student group. Many of the files were also accompanied by dates.
In some cases, the level of detail present might have identified a reporting student to an acquaintance in the same social circles — or potentially to the individual they accused of assault.
In files where the involved parties may be identifiable, the University must notify the individuals. According to Duff, that’s where the University Privacy Office needed to make judgments on just how revealing the previously-accessible information was.
“If the population that fits given descriptions is large enough, no one would be able to identify that person,” Duff said. “It’s a whole field into itself — identification or re-identification of the data so that we can determine who we need to notify.”
Files recording sexual violence cases in a Clery Act folder were generated when an individual or a “Campus Security Authority” — for example, a counselor at Counseling and Psychological Services (CAPS) — filled out a web form created by the University’s Sexual Violence Advisory Board.
While many of the files are based on information disclosed to CAPS, James Jacobs, director of Vaden Health, emphasized that Vaden had no role in managing the Clery report files and that CAPS counseling records, which are separate from Clery data, have not been compromised.
“Vaden clinical records … have been and continue to be completely separate, completely protected and not shared,” he said.
According to Jacobs, CAPS and other entities on campus no longer file Clery reports with the AFS-linked system. Further, he said, CAPS therapists are no longer among the campus entities expected to make Clery reports.
The Clery files, which span from 2012 to 2015, were located within a folder owned by the Stanford University Department of Public Safety (SUDPS). However, according to the University, the summaries of individuals’ cases were not intended for police use or investigation; they were meant solely for fulfilling the University’s duties under the Clery Act, which a non-officer employee of SUDPS oversees.
CAPS’ website states that chart notes from a counseling session — recorded electronically — are kept for 10 years by law but protected with “strict security measures … including physical safeguards, encryption, and password protection.”
The University emphasized that because the Clery reports were generated from a separate process than in-session counseling notes, “SUDPS did not and does not have access to counseling records maintained by CAPS.”
But due to the mistake in the Clery folder’s privacy settings, the text entries to the Clery forms were essentially public.
In some cases, the Clery files potentially shed light on University decisions that confounded and angered many students when they were first announced.
One file described a sexual assault involving two members of the Stanford Band. Another file detailed a student’s account of being sexually assaulted by another student after at a campus event on the Quad.
A handful of files dealt with students who recalled experiences of sexual assault or molestation before they ever came to Stanford.
According to the University, it generally “would have been challenging if not impossible to conduct an investigation” given the high level information recorded in most of the forms.
Confidential University information
Other directories previously left unlocked on AFS include the Office of the President and Provost, the Vice Provost for Student Affairs and Vaden Health Center. Within these folders, however, subfolders and files had varying degrees of privacy.
Files that were accessible included 10-year compilations of University statistics produced each academic year by the Office of Institutional Research and Decision Support. Specific datasets marked as confidential range from statistics on faculty ethnic and gender diversity to detailed breakdowns of financial support for graduate students and levels of government-sponsored activity by school and laboratory.
Some documents include data from other institutions as well, such as a report comparing Stanford with its peer schools on metrics such as median student income, financial aid, research funding sources and faculty diversity. Stanford has since reached out to these schools to apologize for the breach.
Documents like these were not publicly available elsewhere — for example, on the University website — but were unlocked in AFS.
Budget planning resources, as well as memos between then-Provost Condoleezza Rice and the Faculty Senate, were likewise open to anyone with AFS access, including users from other schools.
What is AFS?
Named after Andrew Carnegie and Andrew Mellon of Carnegie Mellon University, the Andrew File System has been in use at Stanford for close to three decades and is also used by a variety of universities and research laboratories. AFS allows a large number of users, each with their own computers, to access a centralized digital workspace owned by their institution or workplace.
Whenever Stanford affiliates log into a desktop machine with their SUNet ID and password, they are accessing the data stored in their personal AFS workspace. For example, students can download useful files into their workspace on a library computer and retrieve that file again when they log in to a dorm cluster computer.
At the same time, AFS allows individuals to use all the institution-owned resources that they are granted access to from their home computers. For instance, computer science majors often use AFS to download and submit homework assignments by entering the directory corresponding to their course.
“Essentially all of my assignments for CS classes are stored there,” said Jorge Ochoa ’18, a computer science major. “I keep my code there for safekeeping and because we have to upload our homework to AFS anyways to turn it in for most classes.”
One of the biggest concerns raised by the AFS data breach: It is hard to know who may have seen or even saved the exposed files during the time that they were accessible.
“I don’t usually need to look for things outside of my personal folders, but I have clicked around a bit either out of curiosity or trying to find class resources which are in a different directory,” Ochoa said.
When asked specifically about the SUDPS and Judicial Affairs files found by The Daily, however, Ochoa said he hadn’t seen any of the information in question.
Andrew Milich ’19, a computer science student who has used AFS for coursework, said that most students doing their homework would probably not stumble into places they shouldn’t be.
“The file system is a little hard to work with,” he said, although he admitted there could be a temptation to browse around. “You kind of have to know what you’re looking for to find something.”
Duff emphasized that any student who finds a security problem in a Stanford system is required by the Honor Code and Fundamental Standard to report the issue immediately to the Information Security Office, the University Privacy Office or another relevant department.
Every institution that employs AFS groups the folders used by its member departments into a single top-level directory. Since AFS was also designed to help different organizations share files, top-level directories are typically visible to users from other organizations that use AFS — meaning that organizations have to take charge of protecting their own information from non-members.
According to Duff, each department at Stanford is responsible for setting its folders and files to the correct accessibility level. That means that the University “relies heavily” on these subgroups to manage their files well. Centralized oversight is difficult, he said, not just for AFS but also for all file-sharing systems, from Dropbox to Google Drive.
“The challenge is how to achieve a zero error rate in the permissions across the hundreds of millions of files [and] folders stored at Stanford,” Duff said.
He added that the sheer scale of the systems needed to store information for an organization the size of Stanford means that each department must take charge of its own security.
The very top-level directory for Stanford, ir.stanford.edu, is overseen by University IT and has the correct settings, according to Duff.
Asked about what support Stanford provides to departments on setting AFS access, Duff pointed to online documentation, saying that “those using AFS are expected to understand how it works.”
However, Duff did describe actions that University IT can take to better ensure information privacy. For one, he said, it can improve awareness about privacy setting issues; right after The Daily informed the University of the incorrectly shared files, Duff emailed Stanford’s over 1,300 IT professionals with a note about the situation and extra tips for managing permissions.
“Inevitably, there are going to be some folks who maybe don’t understand how the permissions work, and they’re not IT people, these are just regular staff members and employees,” Duff said. “Because AFS has been here for so long, I do think there’s an element of, someone else set up the permissions a long time ago and over time just kind of forgot they were open and then other people starting dumping stuff in there.”
According to Duff, a push to move Stanford away from AFS toward other systems such as Box and Google Drive is underway; he hopes the process will prompt departments to review outdated files.
Still, he warned that the permissions errors are not “something there’s a 100 percent solution for.”
“As much as we will try, and we have tried for many years, to do all this stuff right, the scale makes it really tough,” he said.
Duff said that University IT adjusted settings on particular AFS folders to protect the mistakenly public data within two hours of being notified. But cleaning up after the leaks is a longer process. For instance, the University had to request the deletion of cached webpages on Google to prevent people from finding sensitive information even after it was locked.
Potential ramifications
According to Chief Privacy Officer Wendi Wright, the University is “informing individuals in accordance with FERPA and state privacy notification requirements, as applicable.”
Legally, the Family Educational Rights and Privacy Act (FERPA) protects “any information that protects the privacy of student education records” from being shared without written permission.
There are also additional state privacy laws — both statutory and constitutional — covering both students and employees.
According to Robert Rabin, Stanford’s A. Calder Mackay Professor of Law, the University could also be liable to tort lawsuits based on public disclosure of private fact if victims of the data breach can prove that a harm occurred (for example, that their information was accessed and used during the period that it was available).
“There could be two different pathways to responsibility,” Rabin said. “Vicarious liability is where the University is responsible for any branch of the university in violation. The other pathway is negligent supervision, that would be a direct claim that the University should have exercised greater oversight over the branches.”
However, Rabin also said that going into court is an expensive and time consuming process, especially when harms might not be tangible. He was not confident such cases would be pursued, but did stress the significance of the blunder.
“If a vice provost or the department of public safety or whoever is not exercising sufficient caution about protecting student privacy, then the university should be concerned about that,” Rabin said.
In addition to the strictly legal ramifications, Stanford Law Professor and sexual assault activist Michele Dauber worries that there may be consequences for those considering reporting sexual assault in the future.
“One concern that I have is that when survivors find out that Stanford was not adequately safeguarding information that they thought was confidential, they may be even more reluctant to report sexual assault,” she said. “We don’t want students to feel reluctant to report, but an incident like this could have a chilling effect on the willingness of victims to come forward.”
Dauber emphasized that this is especially worrisome given that the last campus climate survey indicated a very low percentage of victims actually report their experiences with sexual assault to anyone at the University.
“The mistake was obviously inadvertent, and I’m sure whoever did it feels terrible about it,” Dauber said. “I’m sure that it wasn’t like Stanford wanted to do this, but this is important, and it’s important to get it right.”
Contact Fangzhou Liu at fzliu96 ‘at’ stanford.edu, Hannah Knowles at hknowles ‘at’ stanford.edu and Ada Statler at adastat ‘at’ stanford.edu.